[NEWS] Azure News of the week
5. Juli 2024Also this week there were many news around Microsoft Azure! Here as always the overview for you: Have fun reading and trying it out…
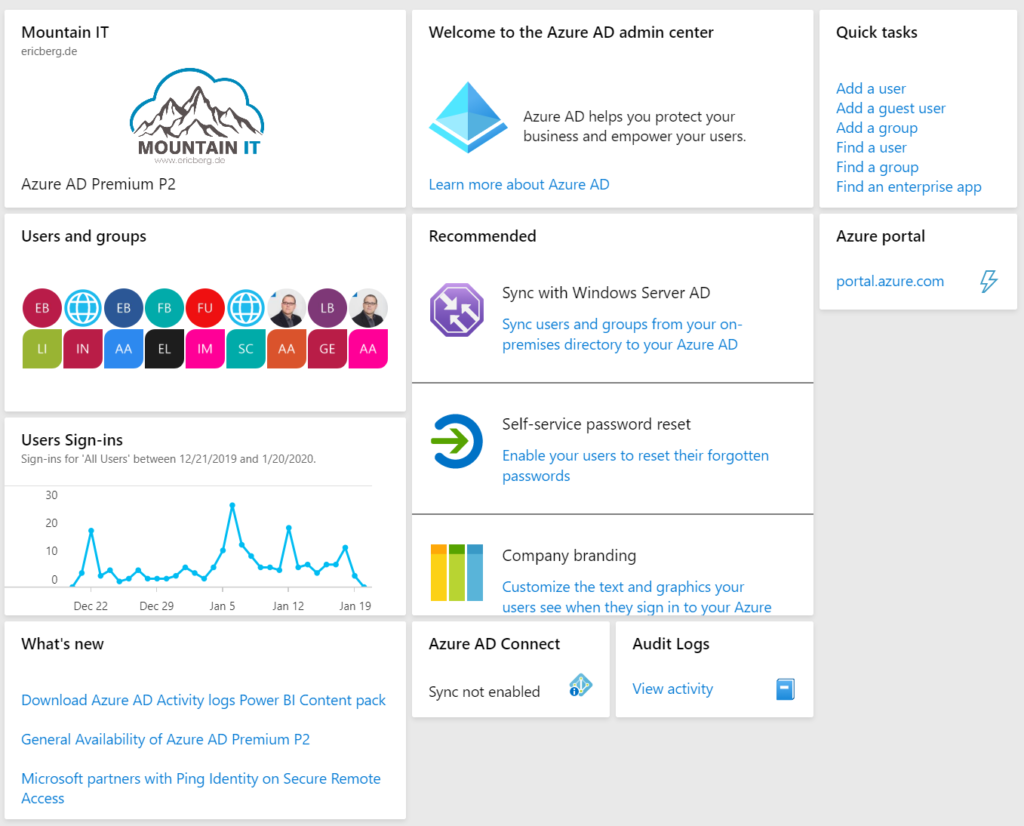
As promised the „BASIC“ articles on this blog will cover fundamental things you need to know. On of the main fundamentals is the Azure Active Directory, or Azure AD, or AAD.
As I see quite a lot of misconceptions out there when it comes to Azure AD, I would like to make sure that everyone understand the importance. Also it is necessary for everyone to know that Azure AD is not „just there“ it is a service, that has to be configured, maintained, and managed.
Azure Active Directory is Microsoft’s cloud-based Identity and Access Management (IAM) Solution. It can be used to sign in to different kinds of internal and external applications. So you can use it to sign in into Software as a Service (SaaS) Solutions like Office 365 or you can use it to authenticate you users to one of your own applications.
When you first sign-up for any Microsoft Service like Azure, Intune or Office 365 then your „Tenant“ will be created. This is your trusted and dedicated instance of Azure AD. It contains your Azure AD Directory. The directory includes your users, groups, apps, …
By default there is one Azure AD per organization. When you sign-up you will create a tenant with a name like „mountainit.onmicrosoft.com“. Every user created in the directory can then sign in via „username@mountainit.onmicrosoft.com“ (or whatever name you had chosen)
Additional to this you can register your own domain, so that for users, they can use their mail address. So the login would change to „username@ericberg.de“ after registering the custom domain „ericberg.de“
And that is pretty much the basic – Azure AD helps to authenticate your users. It has a directory with all your users and groups and handles the authentication.
There are much more features around Azure AD, but this will be a topic later… A nice overview about the options and design decisions for Cloud Identity can be found here: Microsoft cloud identity for enterprise architects
Azure AD is not an implementation of the Windows Server Active Directory Domain Services in the cloud. They have some things in common. Both have a directory for users and groups and take care of authentication and authorization.
But the main difference is how authentication is working. While Windows Server AD is using Kerberos and NTLM, Azure AD was built for web-based authentications like OAuth 2.0 or SAML 2.0.
The other main difference is that with a Windows Server AD you have to take care of the infrastructure. With Azure AD Microsoft is taking care for you.
One thing that you will also miss in Azure AD: Group Policy … but this is another story.
One good thing, you can connect your local Active Directory with Azure Active Directory and make sure that your on-premises users and groups are also provisioned to Azure AD.
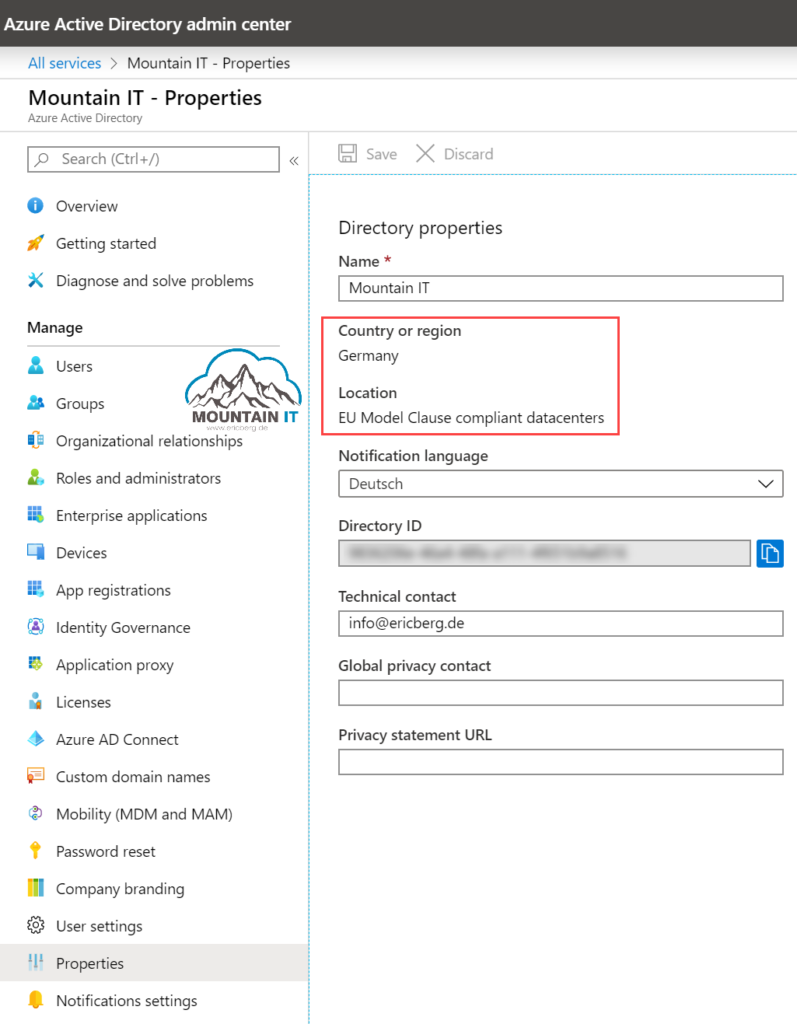
If you want to figure out where your data is stored, then go into the Microsoft Trust Center. There you will find a list of services. When selecting Azure AD you will be redirected to a PowerBI report. That lets you filter for your region and specific services.
If you are from Europe … all Personal Identifiable Information (PII) is stored in Europe. Only for MFA, B2C and B2B datacenters outside of Europe are used. More on this can be found in Docs.
The Region will be chosen based on the location where your contract was signed. or if you signed up via website in self-service… it depends on the location you choose during sign-up.
To check you location afterwards you can go into the properties of your Azure AD … there will find your country and the location of PII Data.
In Azure you need admins to get access to manage your Azure resources. Instead of having a separate User Directory, Azure is using Azure AD for Authentication. You can use your users and groups from AAD and assign them to scopes and resources in your Azure AD. But more on this next week.
To make this happen, every Subscription is attached to an Azure AD.
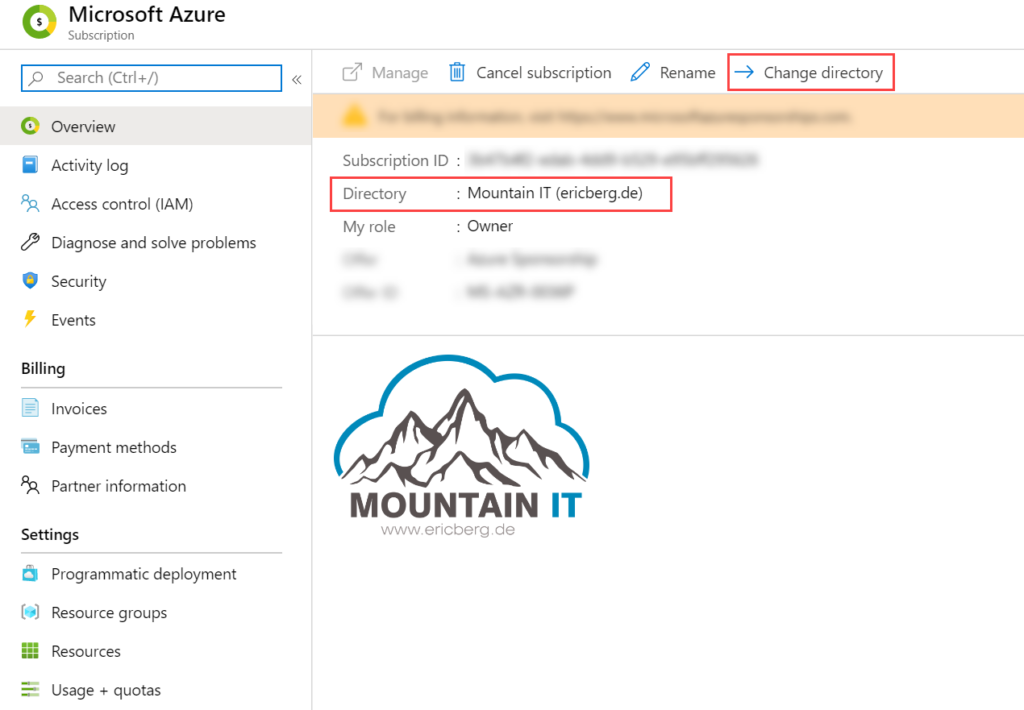
the assigned Azure AD for a subscription is the source of trust to access it. So choose wisely 🙂
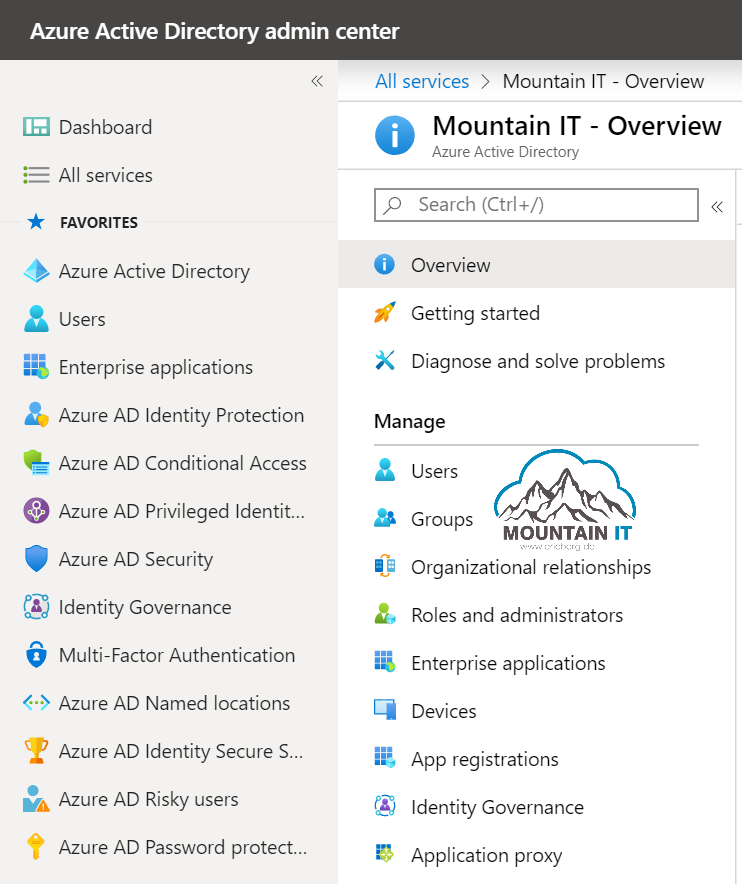
To manage your Azure AD there are multiple ways….and this is causing much confusion. As you can see the users and groups of your Azure AD also in the Office 365 console or in the Intune Management, people sometimes think that there are multiple Azure ADs. Or they even think they require multiple Azure Active Directories.
BUT NO
There is only one Azure AD per organization (normally). It can be associated with multiple services and solutions. So you will have one AAD and will use it to sign-in to Office, Azure, and any other SaaS App.
The main management portal for Azure AD is:
Here you can find everything around Identity and Access Management:
So happy authenticating 🙂
1 Comment
[…] Principals are non personalized accounts. They can get permissions like every other account via Azure AD. The good thing is, that you can assign specific right to this account, needed for the automation / […]